Non classé
Hexagon Unveils “Octave” as Planned Software Spin-Off
Published
4 heures agoon
By

Hexagon AB announced today the launch of a new brand, Octave, marking a key step in a planned spin-off of several of its software businesses. The proposed standalone entity would combine Hexagon’s Asset Lifecycle Intelligence (ALI) division with its Safety, Infrastructure & Geospatial portfolio, alongside the Bricsys, ETQ, and Projectmates businesses.
The separation remains subject to board and shareholder approval, regulatory clearances, and other customary conditions.
If completed, the move would consolidate a broad industrial software portfolio spanning engineering design, construction management, asset performance management, geospatial intelligence, quality systems, and public safety solutions. Octave positions itself around delivering “intelligence at scale” across the full asset lifecycle – from design and build through operation and protection.
Market Implications
The announcement reflects a broader structural trend within industrial technology markets: separating software-centric businesses from diversified parent companies to sharpen focus, accelerate growth, and enhance strategic flexibility. Independent software platforms often gain clearer capital allocation priorities and more targeted product roadmaps.
Octave’s combined portfolio places it firmly in the asset lifecycle and infrastructure intelligence segment – an increasingly competitive space shaped by digital twins, industrial AI, lifecycle data integration, and operational resilience platforms.
By unifying Design, Build, Operate, and Protect capabilities under one structure, the entity would compete more directly with major industrial software providers pursuing end-to-end lifecycle orchestration strategies.
AI and Platform Strategy
Octave’s launch emphasizes domain-specific artificial intelligence embedded across its portfolio. While AI positioning has become ubiquitous in industrial software messaging, competitive differentiation will likely hinge on execution: depth of industry models, integration between engineering and operational data, and measurable performance outcomes in complex infrastructure environments.
As industrial organizations confront aging assets, cybersecurity exposure, regulatory complexity, and volatile supply conditions, software platforms capable of harmonizing engineering, operational, and safety data are increasingly strategic.
If the spin-off proceeds, Octave would emerge as a global industrial software provider with approximately 7,200 employees operating in 45 countries.
Logistics Viewpoints will continue to monitor developments as the separation process advances and further details on strategy, capitalization, and go-to-market positioning emerge.
Read the full release here: Octave Launches New Brand Built Around Unleashing Intelligence at Scale | Octave
The post Hexagon Unveils “Octave” as Planned Software Spin-Off appeared first on Logistics Viewpoints.
You may like
Non classé
Securing Multi-Agent Systems in the Supply Chain: Architecture Before Exposure
Published
4 heures agoon
2 mars 2026By

Artificial intelligence in the supply chain is moving beyond isolated models. We are now seeing coordinated, multi-agent systems managing forecasting, routing, sourcing, inventory balancing, and customer commitments in parallel.
This shift improves speed and responsiveness. It also changes the risk profile.
In a multi-agent architecture, systems communicate, negotiate, and act with limited human intervention. Agent-to-agent coordination, persistent memory layers, and graph-based reasoning create operational leverage. They also expand the attack surface. Security is no longer confined to endpoints or infrastructure. It extends into reasoning chains, trust relationships, and shared context.
As discussed in AI in the Supply Chain: Architecting the Future of Logistics with A2A, MCP, and Graph-Enhanced Reasoning , once AI becomes interconnected, it becomes structural. The same is true of its vulnerabilities.
Multi-agent security is not an IT afterthought. It is an architectural requirement.
Where Multi-Agent Systems Are Vulnerable
Adversarial exploits in multi-agent environments tend to fall into four categories. Each has direct implications for supply chain performance.
1. Data Poisoning and Model Manipulation
Multi-agent systems depend on continuous learning and real-time inputs. If training data or operational data streams are corrupted, agents may draw incorrect inferences without obvious failure signals.
A subtle distortion in demand data can ripple into replenishment decisions. A manipulated supplier performance feed can shift sourcing allocations. These effects often remain latent until a specific interaction exposes the flaw.
In distributed supply chains, detecting poisoned inputs is more difficult because no single model owns the full decision loop. The distortion may only surface when agents coordinate.
2. Communication Interference
Multi-agent architectures rely on constant inter-agent messaging. If those communications are intercepted, delayed, or altered, decision quality degrades quickly.
In practical terms, this might mean:
A routing agent receiving manipulated capacity data
An inventory agent operating on stale shipment updates
A procurement agent reacting to falsified cost signals
Traditional perimeter security does not fully address this. The vulnerability lies in the trust between agents, not just in the network boundary.
3. Byzantine Behavior and Agent Impersonation
In complex multi-agent systems, a compromised or malicious agent can behave inconsistently while appearing legitimate. It may issue conflicting recommendations, introduce biased inputs, or impersonate a trusted actor.
Financial systems have long studied Byzantine fault tolerance. In AI-driven supply chains, the problem becomes more nuanced. The behavior space of agents is vast. Identifying malicious intent requires monitoring logic patterns, not just credentials.
If an agent representing supplier performance is manipulated, sourcing decisions may skew without obvious alarms. If a capacity agent is impersonated, routing decisions may favor incorrect lanes.
Trust in identity is not sufficient. Trust in behavior must be continuously verified.
4. Emergent Exploitation
The most advanced adversarial techniques do not attack individual agents. They exploit emergent behavior that arises from interaction.
In collaborative reasoning systems, one malicious input can subtly steer a group of agents toward a suboptimal or risky outcome. Because the result appears to emerge from consensus, it may be harder to question.
Supply chains are networked systems. Small distortions can cascade. Emergent exploitation targets the network effect itself.
Why Traditional Cybersecurity Falls Short
Legacy cybersecurity models assume defined perimeters, static roles, and deterministic system behavior.
Multi-agent AI environments do not operate this way. They are dynamic, distributed, and adaptive.
Security must therefore shift from protecting infrastructure to protecting reasoning and coordination.
Monitoring server uptime is not enough. Enterprises must monitor how agents decide, how they communicate, and how trust relationships evolve over time.
Building a Defensive Architecture
Securing multi-agent systems requires layered controls embedded into the architecture.
Zero-Trust Agent Identity
Every agent must be uniquely authenticated and cryptographically verifiable. There should be no implicit trust based on network location or historical participation.
Key components include:
Strong identity management for agents
Fine-grained authorization tied to specific functions
Micro-segmentation between agent domains
End-to-end encrypted communications
In a zero-trust model, every interaction is verified. No agent is assumed safe simply because it resides inside the enterprise.
Continuous Adversarial Testing
Multi-agent systems should be tested the way financial institutions test trading platforms, through active simulation.
This includes:
Prompt injection testing
Trust boundary exploitation scenarios
Simulated data poisoning exercises
Cross-agent stress testing
Security teams must evaluate not only individual model robustness but also coordination resilience. The objective is to understand how the system behaves under pressure before a real adversary tests it.
Behavioral Monitoring and Anomaly Detection
Logging is foundational. Every agent action, message, and decision chain should be traceable.
Effective monitoring includes:
Baseline communication frequency and volume
Detection of unusual decision patterns
Identification of logic drift over time
Confidence-based escalation thresholds
In many cases, behavioral deviation is the earliest indicator of compromise.
This is particularly important when persistent memory layers such as Model Context Protocol implementations are in place. If shared context is corrupted, the impact extends across sessions and functions.
Securing the Retrieval and Graph Layers
Many supply chain AI systems rely on retrieval-augmented architectures and increasingly on graph-based structures.
These layers introduce additional considerations:
Knowledge bases must be protected from injection or tampering
Access controls must apply at the entity level in graph systems
Audit trails must capture which documents or nodes influenced a decision
Graph-based reasoning enhances insight. It also increases systemic exposure if improperly governed.
Governance and Accountability
Technology controls are necessary but insufficient. Multi-agent systems require governance discipline.
Enterprises should:
Define where AI is advisory versus autonomous
Establish clear override protocols
Maintain decision audit trails
Involve legal and compliance teams early
Create cross-functional AI oversight committees
In regulated industries, the ability to explain why a routing decision was made or why a supplier was selected is not optional.
Explainability is not just about trust. It is about regulatory defensibility.
The Strategic View
Multi-agent systems represent a structural shift in supply chain operations. They increase coordination speed, reduce manual handoffs, and enable real-time optimization across nodes and networks.
They also concentrate decision power inside interconnected systems.
The question is not whether adversarial techniques will evolve. They will. The relevant question is whether enterprises embed security into the architecture from the outset.
As supply chains adopt agent-to-agent communication, persistent context layers, and graph-enhanced reasoning, security must move in parallel. Identity, behavior, context, and retrieval must all be governed with equal rigor.
Connected intelligence demands connected security.
For supply chain leaders, the path forward is clear:
Architect multi-agent systems deliberately
Do penetration testing
Adopt continuous monitoring
Govern them transparently
Performance gains without security discipline create systemic exposure.
Resilient supply chains will not only be intelligent. They will be defensible by design.
The post Securing Multi-Agent Systems in the Supply Chain: Architecture Before Exposure appeared first on Logistics Viewpoints.
Non classé
IFS Acquires Softeon: Shifting the Tides of Warehouse Management Systems and Supply Chain Software
Published
6 heures agoon
2 mars 2026By

On March 2, 2026, IFS announced the completion of its acquisition of Softeon, formally combining the two companies under the banner IFS Softeon.
While acquisitions in supply chain software are not unusual, this transaction is notable for what it suggests about the evolving role of warehouse management within broader enterprise platforms.
Rather than positioning warehouse management as a standalone operational system, IFS is clearly framing Softeon as a core execution component within a larger, AI-enabled enterprise architecture.
Closing the Gap Between Planning and Execution
A persistent theme in supply chain software over the past decade has been the disconnect between enterprise planning systems and execution systems on the warehouse floor. ERP platforms have traditionally focused on planning, financial control, and master data, while WMS platforms have optimized inventory movement, picking, and shipping. According to IFS, this separation has created “blind spots” between strategic decision-making and physical execution.
The Softeon acquisition directly addresses this issue. Softeon brings more than 20 years of experience delivering tier-one warehouse management software, while IFS contributes its Industrial AI capabilities and enterprise platform designed for asset-intensive industries. The combined offering is positioned as providing visibility “from the boardroom to the warehouse floor,” a phrase that reflects a growing industry emphasis on linking operational execution data to enterprise-level decision-making.
Softeon’s Position in the Warehouse Software Landscape
Softeon has historically occupied a distinct position in the warehouse management market. Beyond core WMS functionality—such as inventory control, order management, and labor tracking—Softeon has invested heavily in execution-oriented capabilities, including real-time orchestration of labor and automation.
Internal research consistently highlights that traditional WMS platforms struggle in environments characterized by high automation, robotics, and rapidly changing execution priorities. In these settings, execution logic increasingly shifts toward systems that can dynamically sequence work, balance labor and machines, and respond to real-time conditions on the warehouse floor. Softeon’s technology portfolio aligns closely with this trend, particularly in complex distribution and omnichannel fulfillment environments.
The press release notes that Softeon manages warehouse operations for a range of large, global customers and operates across more than 30 countries, processing millions of orders per month. This installed base gives IFS immediate credibility in warehouse-centric industries where it previously played a more limited role.
IFS and the Expansion of Industrial AI into Warehousing
IFS has traditionally been associated with enterprise applications for manufacturing, asset management, and service management. Its messaging around Industrial AI emphasizes domain-specific intelligence embedded directly into operational workflows, rather than generic analytics layered on top of transactions.
By acquiring Softeon, IFS extends this Industrial AI narrative into warehouse operations. Warehouses increasingly serve as critical nodes in supply chains, particularly as companies pursue faster fulfillment, higher service levels, and greater resilience. Execution data generated in warehouses—such as labor productivity, automation utilization, and order flow constraints—represents an underutilized source of insight for enterprise decision-making.
IFS states that its customers collectively manage trillions of dollars in critical assets and operate at massive scale across industries such as aviation, manufacturing, and logistics. The addition of Softeon allows IFS to incorporate warehouse execution data into this broader operational context, potentially strengthening its value proposition as an end-to-end enterprise platform.
Market Implications
From a market standpoint, the formation of IFS Softeon reflects several broader trends identified in internal research:
Convergence of ERP, WMS, and execution systems as customers seek fewer integration points and more unified data models
Rising importance of real-time execution intelligence, particularly in automated and hybrid warehouses
Increased demand for single-vendor accountability across planning, execution, and optimization layers
Rather than competing solely as a WMS provider, IFS Softeon enters a competitive landscape that spans enterprise software vendors, traditional WMS suppliers, and execution-focused platforms. The differentiation will likely hinge on how effectively IFS can integrate Softeon’s execution strengths with its existing AI and enterprise capabilities.
Bottom Line
The acquisition of Softeon by IFS is best viewed not as a simple expansion into warehouse management, but as a strategic move to bring execution intelligence deeper into the enterprise stack. As supply chains become more automated, time-sensitive, and disruption-prone, the ability to connect warehouse execution with enterprise decision-making is becoming a competitive requirement rather than a differentiator.
The post IFS Acquires Softeon: Shifting the Tides of Warehouse Management Systems and Supply Chain Software appeared first on Logistics Viewpoints.
Non classé
When Supply Chain Decisions Carry Consequences – The New Logistics Viewpoints
Published
9 heures agoon
2 mars 2026By

Today we relaunch Logistics Viewpoints as an institutional decision-support platform for supply chain technology leaders.
This is not a cosmetic redesign. It is a structural repositioning.
The site is now organized around decision-relevant domains that mirror how supply chains are actually designed, automated, capitalized, and governed. Planning. Transportation. Warehousing. Global Trade. AI. Data Architecture. Industrial Platforms. Risk. Sustainability.
No noise.
No trend chasing.
No volume for its own sake.
Our objective is clarity in consequential decisions — platform selection, automation strategy, AI architecture, market positioning, and capital allocation.
Explore the platform:
Home
https://logisticsviewpoints.com/
Research
https://logisticsviewpoints.com/research/
Topics
https://logisticsviewpoints.com/topics/
Logistics Viewpoints reflects the analytical discipline of ARC Advisory Group and is written for leaders who carry investment accountability.
When decisions carry operational or financial consequence, structured analyst engagement reduces risk and accelerates alignment.
Engage Analysts
https://logisticsviewpoints.com/engage-analysts/
Logistics Viewpoints is not designed to maximize clicks.
It is designed to improve decisions.
Independent. Structured. Decision-Focused.
— Jim Frazer
The post When Supply Chain Decisions Carry Consequences – The New Logistics Viewpoints appeared first on Logistics Viewpoints.


Securing Multi-Agent Systems in the Supply Chain: Architecture Before Exposure

Hexagon Unveils “Octave” as Planned Software Spin-Off

IFS Acquires Softeon: Shifting the Tides of Warehouse Management Systems and Supply Chain Software

Walmart and the New Supply Chain Reality: AI, Automation, and Resilience
Ex-Asia ocean rates climb on GRIs, despite slowing demand – October 22, 2025 Update
13 Books Logistics And Supply Chain Experts Need To Read
Trending
-

 Non classé12 mois ago
Non classé12 mois agoWalmart and the New Supply Chain Reality: AI, Automation, and Resilience
- Non classé4 mois ago
Ex-Asia ocean rates climb on GRIs, despite slowing demand – October 22, 2025 Update
- Non classé7 mois ago
13 Books Logistics And Supply Chain Experts Need To Read
- Non classé1 mois ago
Container Shipping Overcapacity & Rate Outlook 2026
- Non classé4 mois ago
Ocean rates climb – for now – on GRIs despite demand slump; Red Sea return coming soon? – November 11, 2025 Update
- Non classé1 an ago
Unlocking Digital Efficiency in Logistics – Data Standards and Integration
-

 Non classé7 mois ago
Non classé7 mois agoBlue Yonder Acquires Optoro to Revolutionize Returns Management
-
 Non classé5 mois ago
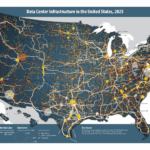
Non classé5 mois agoNavigating the Energy Demands of AI: How Data Center Growth Is Transforming Utility Planning and Power Infrastructure
